How to detect and remove spyware PC Pandora
PC Pandora belongs to the class of spyware running via DLL libraries. This is a fairly rare type of user’s tracking software, and they are good at hiding their presence on the computer. This program does not have a folder in which it stores its data. All components of this program are loaded into the operating system, and each new installation on the same or another computer made with new file names. For this reason, it is not always possible to identify it as a spyware. This program has no processes, services, drivers, and it’s not in the startup and standard locations where you can run the software. It uses DLL libraries, one of which loads with the operating system and through it connects the other. PC Pandora does not affect the performance of the computer, so you do not suspect anything.
Obviously, it is difficult to find this program on your computer by classical methods of protection, as their most reliable tool is the signature database, and PC Pandora uses different data on each computer.
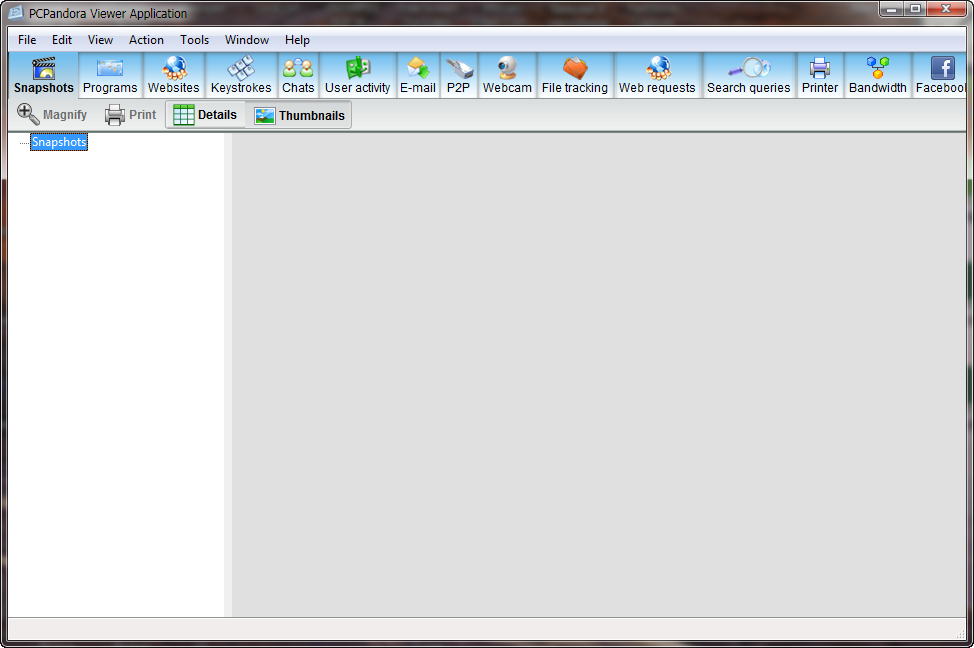
If we consider the positioning of the program as a tool for parents wanting to know what their children are doing online, and for managers wishing to catch careless employees wasting working time, the spy PC Pandora may not get to the list of dangerous programs.
We believe that not only parents and supervisors are the target group for this spyware.
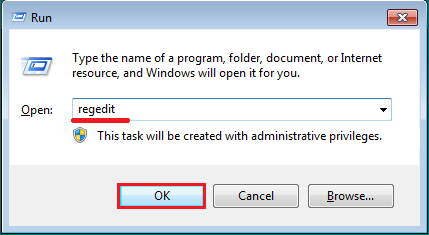
So, run COVERT Pro and click on the button “DLL Monitor” in the main menu. Then disable in context menu User Account Control (UAC), if it is enabled.
(UAC is a security feature of Windows which helps prevent unauthorized changes to your computer.)
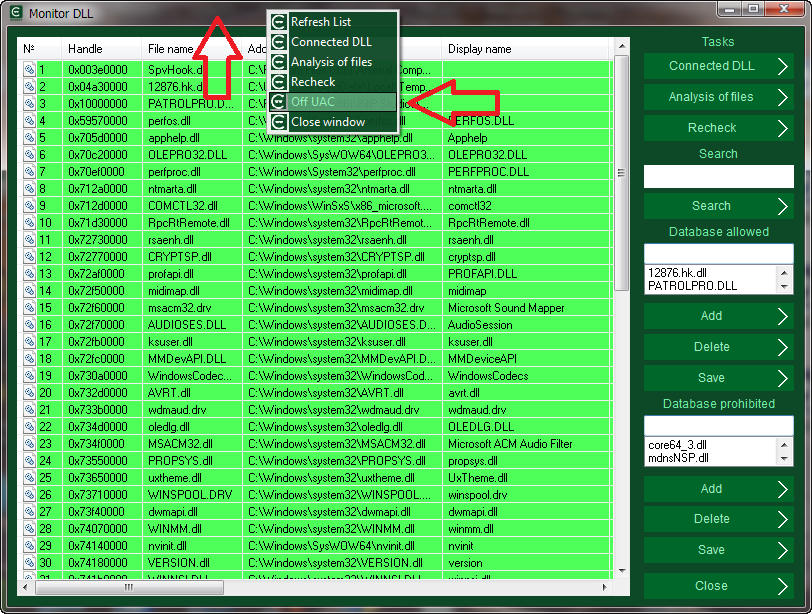
COVERT Pro and its monitors work with administrator rights. Not all spyware can be connected to programs with such rights. To see all libraries, you should disable UAC during the system analysis. Later, in the same way, UAC can be enabled.
If you use the version COVERT Pro USB, then disable UAC for analysis of the monitor DLL is not required. When you start the program you just need to refuse using administrator rights.
Restart your computer, run COVERT Pro and open the Monitor DLL.
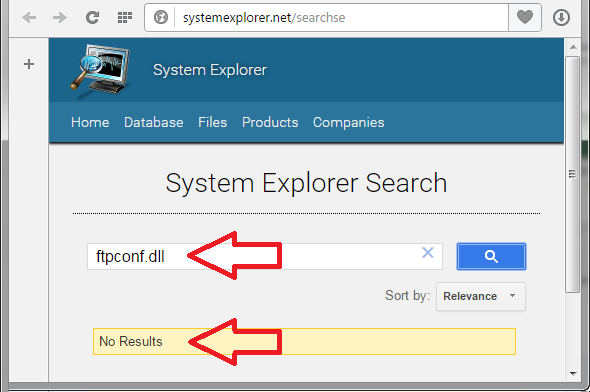
In the list of loaded libraries, we see two libraries highlighted in yellow – ftpconf.dll and usbweb.dll located in the system folder. This file belongs to PC Pandora. We know this because we installed it in the system.
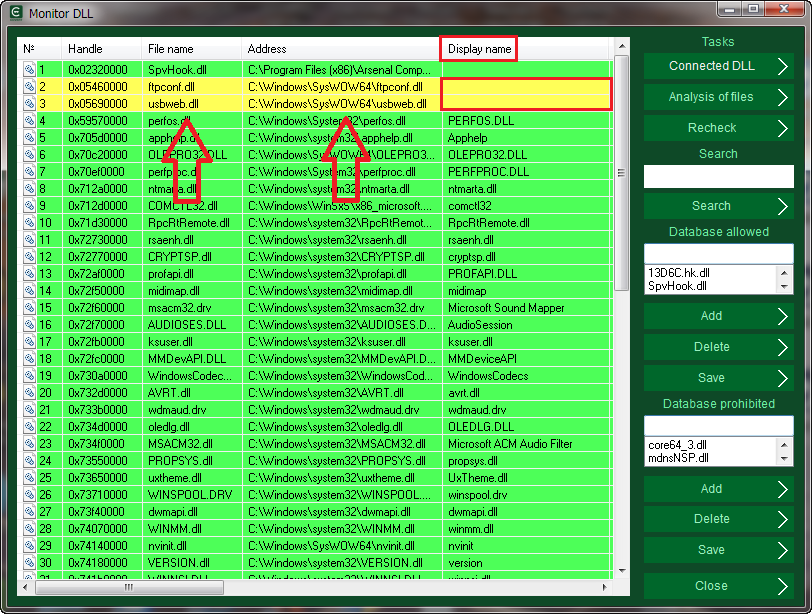
If we didn’t do this experiment, but we found such libraries in the Monitor DLL, then we would need to figure out – which program they belong to. Using the context menu, select “Search for information in Internet“.
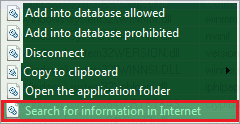
We see that there is no information about these libraries. They do not belong to operating system or other software installed by the user.
Moreover, filenames of these libraries are specified by the developer of the program, but not by the OS. There are no description, version number and the name of the developer company. Therefore, even if we did not know that the DLL files belong to PC Pandora, they should be removed anyway.
Spyware PC Pandora was detected. Now let’s look at how to remove it.
Right click on the yellow line in the context menu and select disable. In the message that appears, confirm our intentions. Do the same thing with the second file.
To complete removal of spyware you have to restart your computer. After restarting your computer, PC Pandora will be neutralized.
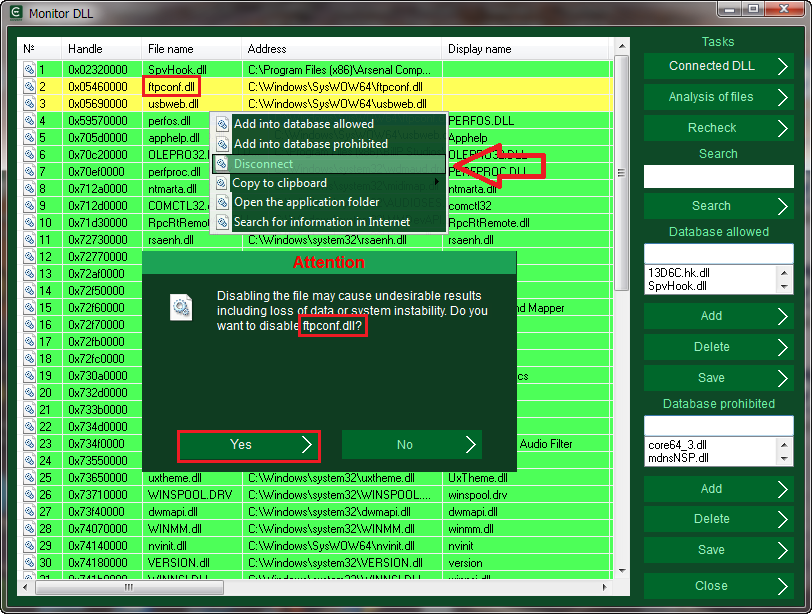
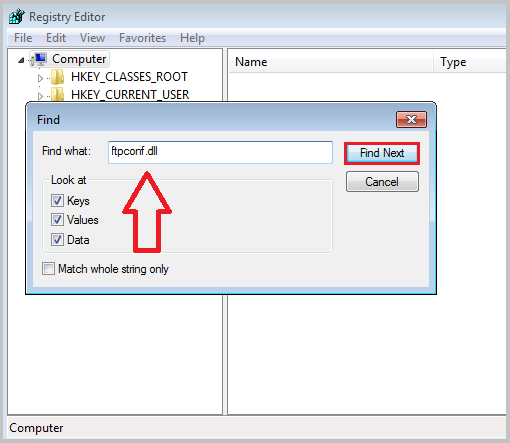
If an error message appears, open the registry. To do this, click on the keyboard Win + R keys, enter regedit and press Ok.
Using the search function find and remove all parameters that contain the name of the spyware library ftpconf.dll
To hide user’s actions from the spy PC Pandora, without removing it from your computer, enter the secure platform by clicking on the large button with the logo and the inscription “Login to the secure platform“.
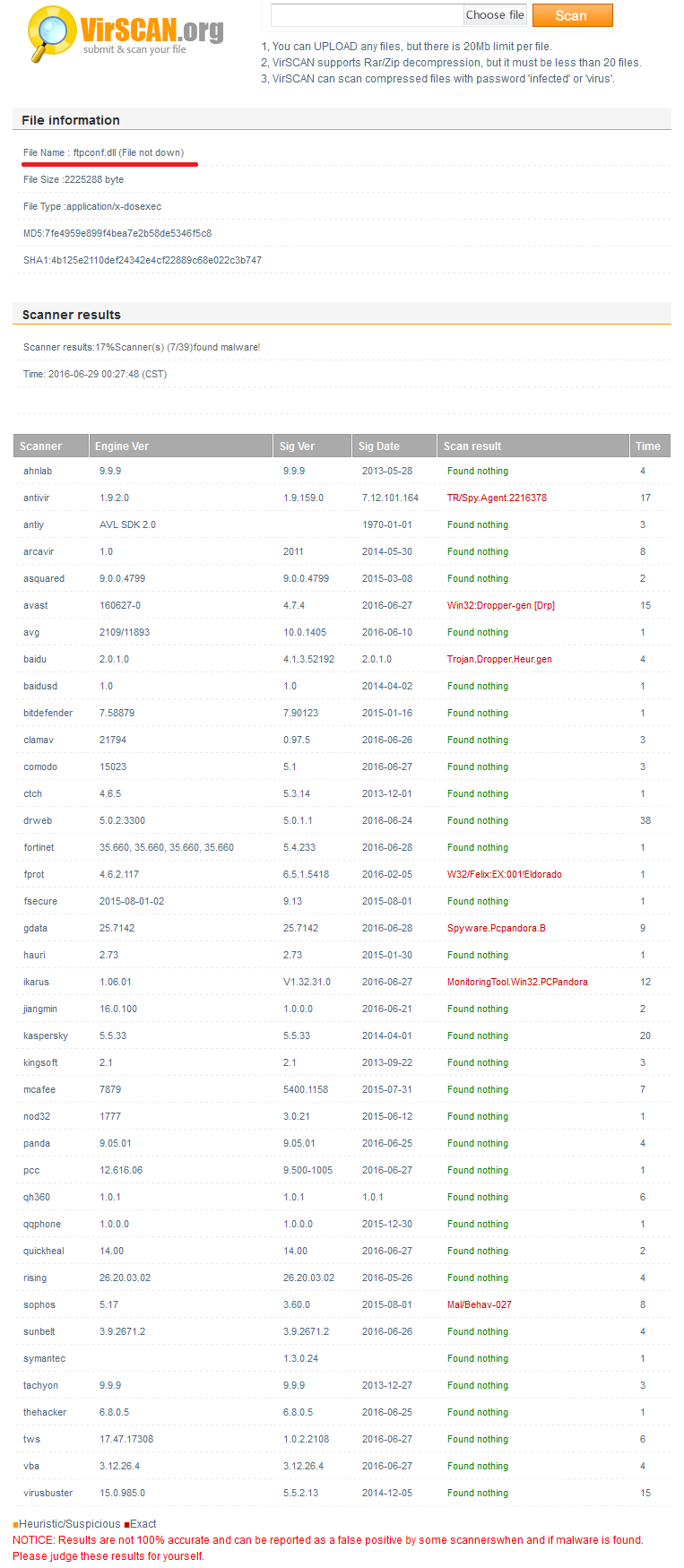
We have checked file ftpconf.dll on one of the most popular online services using 39 antivirus programs. Only seven of them were able to find a threat in this spyware.
Download COVERT Pro and check FREE of charge your computer for spyware and rootkits, which were not detected by an antivirus.