VkurSe

It is hard to detect VkurSe using standard tools, but COVERT Pro has enough tools to detect the most sophisticated spies.
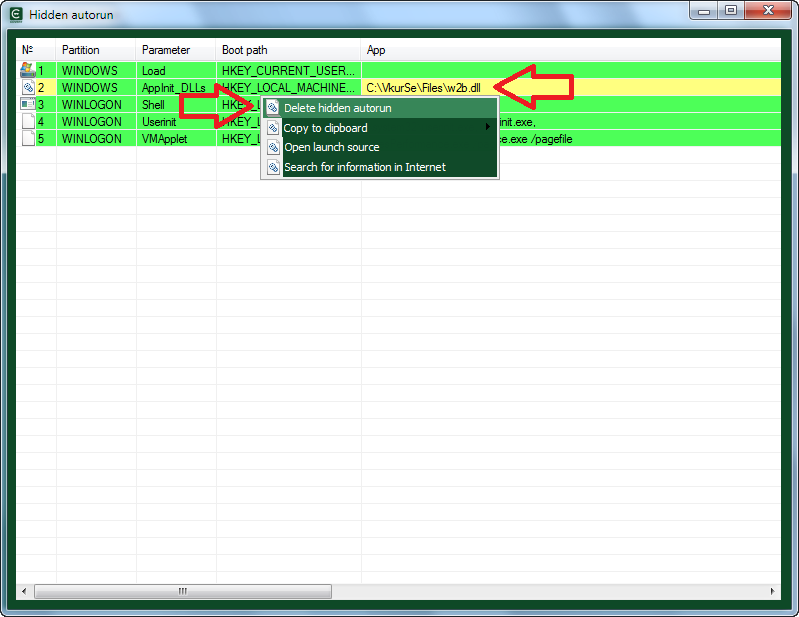
Open the “Autoload Monitor”, click on the “Hidden autorun” button and in the list of applications which are launched along with the operating system, we can see the line highlighted in yellow. This is the w2b.dll library, which belongs to the spy VkurSe (DLL is a library that contains code and data that can be used simultaneously by more than one program.)
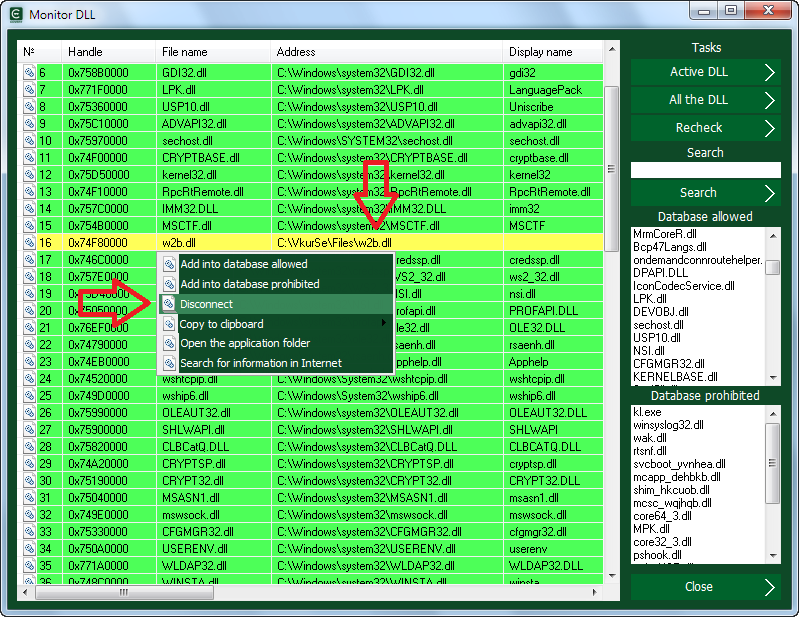
The w2b.dll library is intend to establish various hooks and intercepts in the system. We can also see it in the library monitor. When we open the “Monitor DLL”, we can see the same name without identifiable names, descriptions and other data. It is also highlighted in yellow.
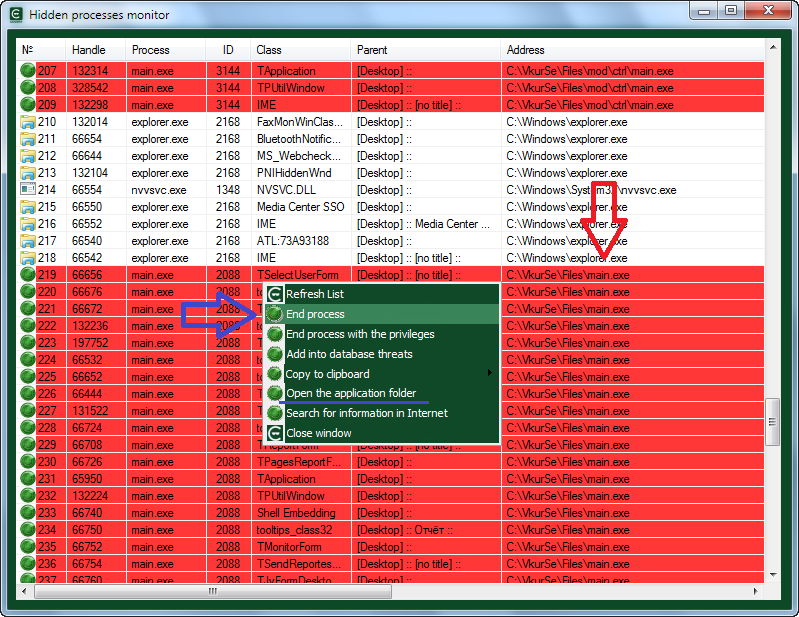
The main purpose of this library is to load itself and the main.exe process together with the operating system. By the way, this process is visible only in the list of hidden processes. Open the window
“System processes” and then “Hidden processes”.
All lines with this process are highlighted in red because it is hidden in the OS.
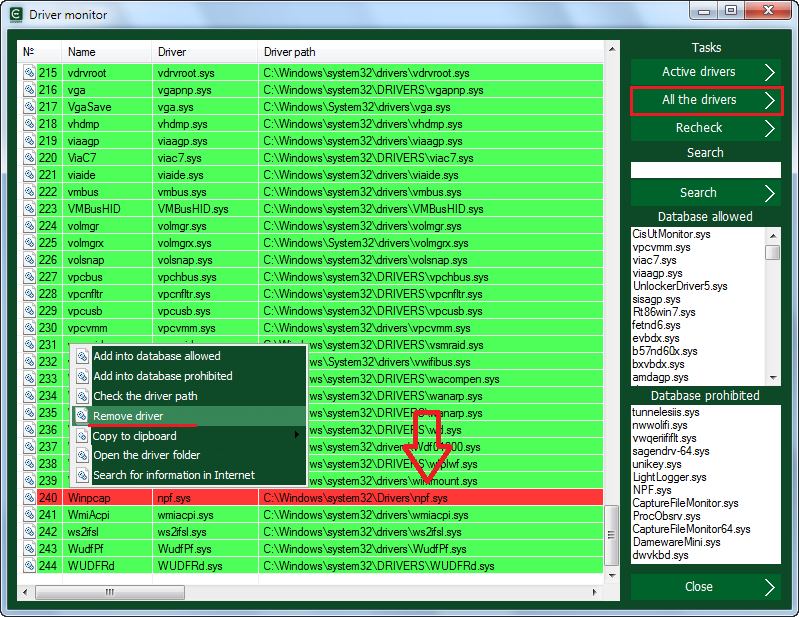
There is another spy module – the npf.sys driver. It is highlighted in red in the “Driver Monitor” because it is already listed in the database of threats. This driver is in use by many spyware programs that we have tested in our laboratory.
Since this spyware can send stolen information via Internet, the “main.exe” process is visible during data transfer in the network monitor (if this process is not already included in the database of threats).
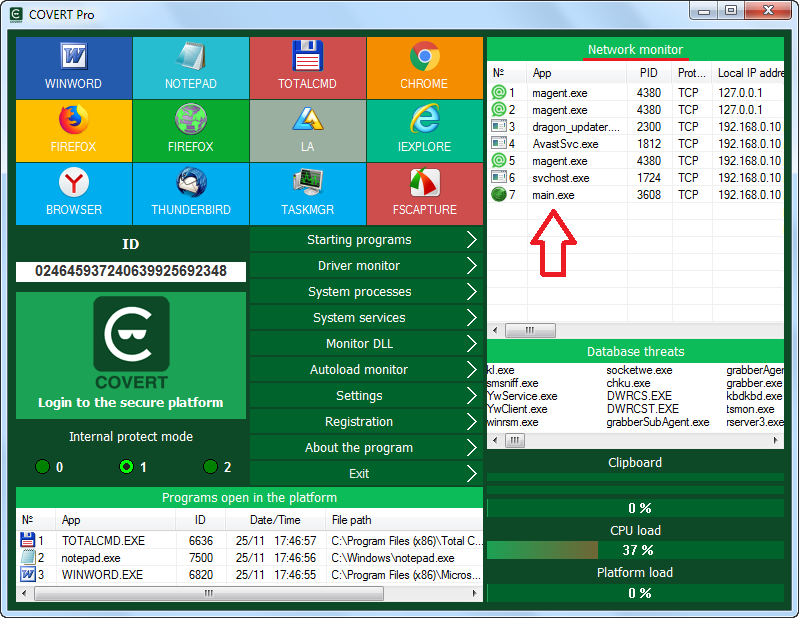
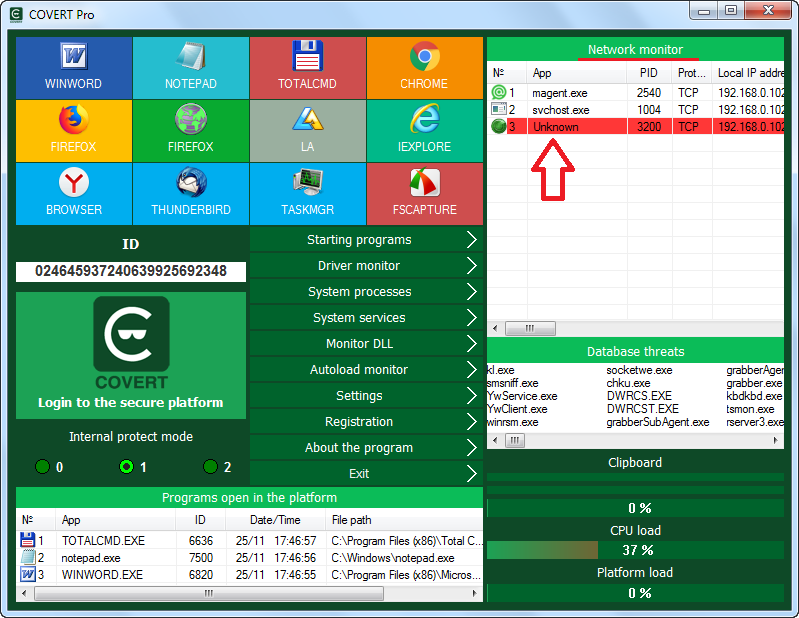
Main.exe will be highlighted in red if it is blocked by COVERT Pro (it happens if the name of the spy process is added to the database of threats) or in case when the spy hides itself and cannot be identified.
In this case, it gets the name “Unknown”. All unknown processes are blocked by COVERT Pro by default. This happened during VkurSe test. After spyware process is blocked, an attacker will not be able to spy and receive stolen information.
The screenshots above show the steps for removing VkurSe spyware. All actions are performed using the context menu (right-click).
Here is the list of necessary steps:
1. Delete the hidden autorun library w2b.dll (in the monitor of hidden autoload).
2. Shutdown the w2b.dll library (monitor DLL).
3. Open the application folder and terminate the hidden spy process main.exe (in the monitor of hidden processes).
4. Remove the npf.sys driver (in the monitor of drivers).
5. Completely delete the folder with all spyware files that was opened through the context menu in step 3.
6. Restart your computer and check all COVERT Pro monitors that may contain information about this spyware.
If you don’t remove all the spyware modules, you still can protect your information by working in COVERT Pro protection platform (click large button with the logo and the inscription: “Login to the secure platform”). VkurSe will not be able to intercept and save all your actions. Spyware log will be empty.
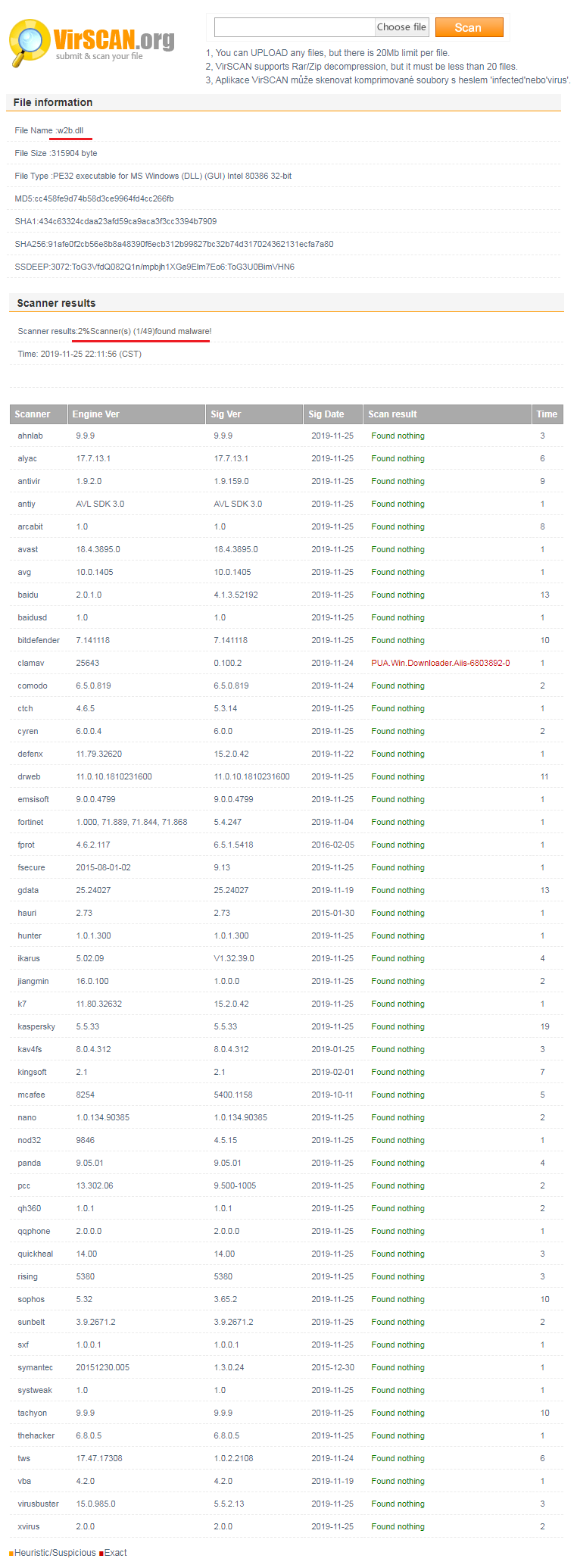
Traditionally we check spyware on virscan.org. Only one of the 49 antiviruses detected that w2b.dll library is dangerous to the user. Therefore, you are unlikely to find it without COVERT Pro if someone is interested in your information and you have this spyware installed on your computer.
We rate this spyware program as RLM: 5 / 5 / 4.
Download COVERT Pro and check FREE of charge your computer for spyware and rootkits, which were not detected by an antivirus.